Every time you type a web address, your browser trusts a chain of servers to send you to the right place. But what if that chain was poisoned? DNSSEC exists to stop exactly that — and understanding its importance could protect you, your business, and the internet itself.
Here's a terrifying truth about the internet: the system that directs your browser to the right website was designed in the 1980s — and it was never built with security in mind. For decades, it had no way to verify whether the answers it gave you were real. DNSSEC was created to fix that. And its importance has never been greater.
Let’s pull back the curtain on one of the most critical — and most overlooked — layers of internet security.
First, a Quick Refresher: What Is DNS?
Before we can understand DNSSEC, we need to understand the system it protects.
The Domain Name System (DNS) is the internet’s phonebook. When you type yourbank.com into your browser, your computer doesn’t actually know where that website lives. It sends a query to a DNS resolver, which looks up the IP address — say, 203.0.113.42 — and sends your browser there.
This happens in milliseconds, billions of times a day, for every website visit on the planet.
The problem: The original DNS protocol has no authentication. When your computer asks “where is yourbank.com?” and gets an answer back, it has no way to verify whether that answer is genuine. It simply trusts it. And that trust is exactly what attackers exploit.
So What Is DNSSEC?
DNSSEC stands for Domain Name System Security Extensions. It is a suite of Internet Engineering Task Force (IETF) specifications that adds a layer of cryptographic authentication to DNS.
In plain English: DNSSEC lets your computer verify that the DNS answer it received is genuine — that it actually came from the authoritative source and hasn’t been tampered with in transit.
Think of it this way. DNS without DNSSEC is like receiving a letter with no sender address and no signature. You have no way to know if it’s real. DNSSEC adds a wax seal and a verified signature — proof that the letter is authentic and hasn’t been opened along the way.
1997
DNSSEC was first proposed by IETF
2010
Root zone signed with DNSSEC
~40%
Of DNS queries globally validated by DNSSEC
90%+
Of top-level domains signed with DNSSEC
$Bn
Lost annually to DNS-based cyberattacks
The Threat DNSSEC Was Built to Stop: DNS Cache Poisoning
To understand the full importance of DNSSEC, you need to know about DNS cache poisoning — one of the most dangerous and invisible cyberattacks in existence.
Here’s how it works:
- Your computer asks a DNS resolver: “Where is mybank.com?”
- Before the real answer arrives, an attacker injects a fake answer: “mybank.com is at this IP address” — an IP they control.
- The resolver caches (stores) this fake answer and serves it to everyone who asks.
- You type mybank.com, your browser goes to a perfect-looking fake site, and you hand over your login credentials.
- You never see any warning. Your browser shows the correct address in the URL bar.
The Kaminsky Attack (2008): Security researcher Dan Kaminsky discovered a devastating flaw that allowed attackers to poison DNS caches at massive scale — affecting virtually every DNS resolver on the internet. It was one of the most alarming security disclosures in internet history and became the single biggest catalyst for DNSSEC adoption.
What Attacks Does DNSSEC Protect Against?
The importance of DNSSEC goes beyond just cache poisoning. Here are the major attack categories it defends against:
DNS Cache Poisoning
Injecting false DNS records into resolver caches to redirect users to malicious sites without their knowledge.
Man-in-the-Middle
Intercepting DNS queries in transit and returning forged responses to hijack traffic silently.
DNS Spoofing
Sending fraudulent DNS responses impersonating legitimate name servers to deceive resolvers.
Pharming
Redirecting users from legitimate sites to fake clones at scale — often targeting financial or government sites.
BGP Hijacking + DNS
Combining routing attacks with DNS manipulation to perform sophisticated, large-scale traffic interception.
Replay Attacks
Reusing captured DNS responses to repeatedly fool resolvers — DNSSEC’s signatures prevent this by design.
How Does DNSSEC Actually Work?
DNSSEC uses public-key cryptography to create a chain of trust from the DNS root all the way down to individual domain records. Here’s the process broken down into clear steps:
ve scale — affecting virtually every DNS resolver on the internet. It was one of the most alarming security disclosures in internet history and became the single biggest catalyst for DNSSEC adoption.
ZONE SIGNING
The domain owner signs all DNS records in their zone using a private key, generating digital signatures (RRSIGs) for each record.
KEY PUBLICATION
The corresponding public keys (DNSKEY records) are published in the DNS zone so anyone can verify signatures.
Delegation Signing
A DS (Delegation Signer) record is submitted to the parent zone, linking this zone’s keys into the global chain of trust.
ROOT ANCHOR
The chain climbs all the way to the DNS root zone, signed by ICANN’s Root Zone Signing Key — the ultimate trust anchor.
VALIDATION
When your resolver receives a DNS answer, it checks the signature against the public key. Tampered = rejected. Authentic = accepted.
Authenticated Denial
DNSSEC can also cryptographically prove that a domain does NOT exist — preventing attackers from faking non-existent records.
Key Record Types in DNSSEC
DNS Key
Holds the public signing key for a DNS zone. Used by resolvers to verify digital signatures.
RRSIG
Resource Record Signature. The cryptographic signature attached to each signed DNS record set.
DS
Delegation Signer. Links a child zone’s key to the parent zone, forming the chain of trust upward.
NSEC/NSEC3
Next Secure Records. Cryptographically prove the non-existence of a DNS name — blocking fake “not found” attacks.
What a Signed DNS Response Looks Like
; DNSSEC-signed DNS response example
example.com. 300 IN A 93.184.216.34
example.com. 300 IN RRSIG A 8 2 300 (
20260415000000 20260315000000 12345 example.com.
abc123XYZsignatureDataHere== )
example.com. 3600 IN DNSKEY 256 3 8 (
publicKeyDataHere== )
The RRSIG signature is checked against the DNSKEY. If they match — and if the DNSKEY is trusted via the DS chain — the answer is authentic. If anything was tampered with in transit, the signature fails and the response is rejected.
“DNSSEC doesn’t encrypt your DNS traffic — it authenticates it. The difference could save your business from catastrophe.”
A Critical Distinction: DNSSEC vs. HTTPS vs. DNS over HTTPS
People often confuse these three. They’re all important, but they do very different things:
- DNSSEC — authenticates DNS records. Proves the answer you received is genuine and untampered. Does not encrypt the query.
- HTTPS / TLS — encrypts the connection between your browser and a website. Protects data in transit. Does not authenticate DNS.
- DNS over HTTPS (DoH) / DNS over TLS (DoT) — encrypts the DNS query itself so eavesdroppers can’t see what sites you’re looking up. Does not authenticate DNS answers.
The gold standard: All three layers working together — DNSSEC to authenticate answers, DoH/DoT to encrypt queries, and HTTPS to secure the connection. Each one fills a gap the others cannot.
The Real-World Importance of DNSSEC: Why It Matters
The importance of DNSSEC isn’t theoretical. Real attacks with real consequences happen every year because DNS remains unprotected on millions of domains.
- 2019 — Sea Turtle Campaign: State-sponsored hackers hijacked DNS records of government and military agencies across the Middle East and North Africa, redirecting traffic to steal credentials. DNSSEC could have detected and blocked these redirections.
- 2020 — Brazilian Banks: Attackers poisoned DNS to redirect customers of major Brazilian banks to convincing phishing clones, harvesting millions in credentials. None of the targeted domains had DNSSEC enabled.
- 2021 — BGP + DNS Hijacks: Multiple cryptocurrency platforms suffered DNS hijacking attacks that drained millions of dollars from user wallets by redirecting to fake sites.
- 2023 — Government Portals: Several national government portals in Asia and Africa were compromised via DNS manipulation, exposing citizen data and eroding public trust.
DNSSEC Adoption: Where Are We Now?
The good news is that adoption is growing. The bad news is it still has a long way to go — especially at the individual domain level.
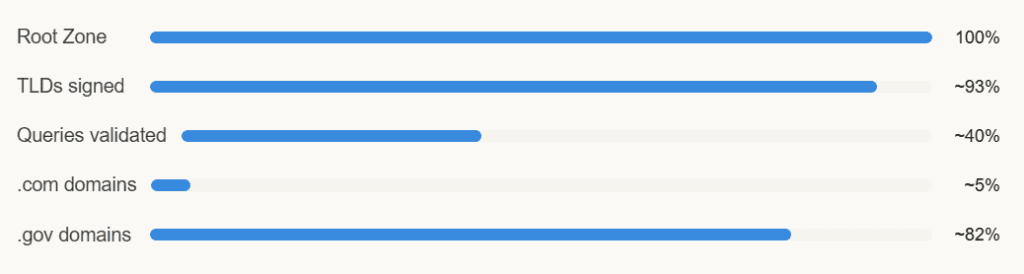
The gap between TLD signing (93%) and individual .com domain signing (~5%) is where most of the risk lives. Millions of websites — including banks, e-commerce stores, and email providers — remain unsigned and vulnerable.
Challenges Slowing DNSSEC Adoption
If DNSSEC is so important, why isn’t everyone using it? Here are the honest barriers:
- Complexity of deployment: Signing a zone, managing key rollovers, and maintaining DS records requires technical expertise many small businesses don’t have.
- Key management overhead: Cryptographic keys must be rotated regularly. Mishandling a rollover can make a domain completely unreachable.
- Larger response sizes: DNSSEC adds data to DNS responses, which can cause issues with older or restrictive network configurations.
- False sense of HTTPS security: Many admins assume HTTPS alone is enough — without realising DNS can be poisoned before HTTPS even gets a chance to kick in.
- Limited registrar support: Not all domain registrars make DNSSEC easy to enable — some don’t support it at all.
How to Check If Your Domain Has DNSSEC Enabled?
You can test any domain in seconds using free tools. The most widely used is ICANN’s own DNSSEC Analyzer or Verisign’s DNSSEC Debugger. Simply enter your domain and look for a chain of validated green keys from the root down to your domain record.
- Visit dnssec-analyzer.verisignlabs.com — enter your domain name
- Visit dnsviz.net — visual chain-of-trust diagram for your domain
- Run dig +dnssec yourdomainname.com in a terminal to check for RRSIG records
- Check your domain registrar’s DNS settings panel for a DNSSEC toggle or DS record option
- Contact your DNS hosting provider to confirm DNSSEC signing is active on your zone
Quick Recap: Why the Importance of DNSSEC Cannot Be Overstated
- DNS was built without authentication — DNSSEC fixes that with cryptographic signatures
- It protects against cache poisoning, spoofing, pharming, and man-in-the-middle attacks
- It works by creating an unbroken chain of trust from the DNS root to your domain
- It complements — but does not replace — HTTPS, DoH, and other security layers
- Real-world attacks costing billions annually could be mitigated with DNSSEC adoption
- Root and TLD adoption is strong; individual domain adoption urgently needs to catch up
- Tools exist to check and enable DNSSEC for your domain today — for free
Don’t Leave Your Domain Unsigned — Check It Today
Every day your domain runs without DNSSEC is a day attackers can redirect your visitors to phishing sites without a single warning. The importance of DNSSEC isn’t abstract — it protects your users, your reputation, and your data. Take five minutes right now.Enable DNSSEC on My Domain ↗
Share this post with your web developer or IT team — they need to read it.